

Tired of manually validating vulnerabilities?
Stop
wasting time on complex penetration-testing workflows.
Online Automated Penetration Testing System: Replicates
the complete hacker attack chain — from information
gathering, vulnerability exploitation to privilege
escalation. One-stop intelligent management,
full-process penetration testing control.
Input a
target, get an in-depth penetration report instantly.
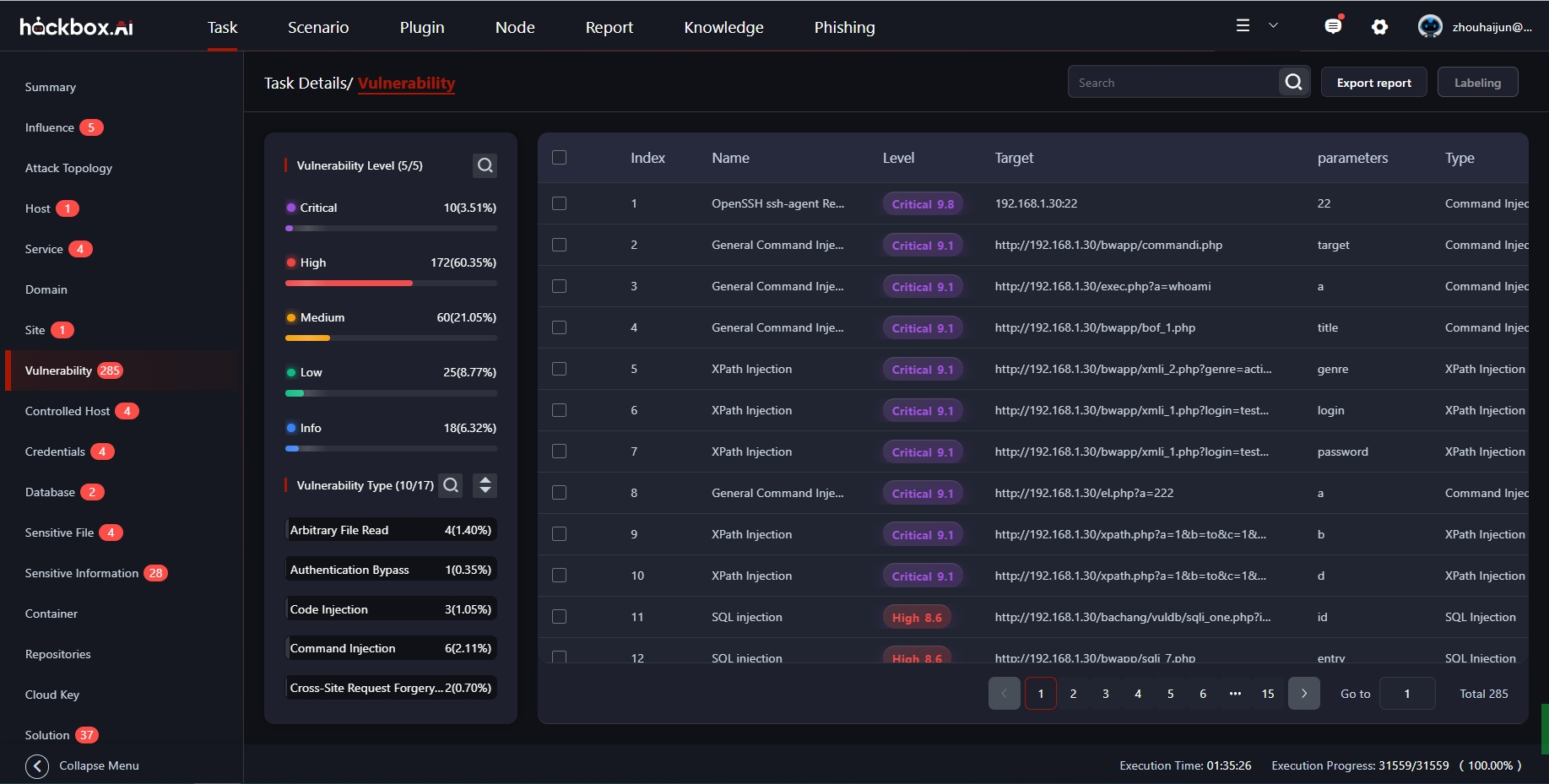
Our platform delivers comprehensive security validation and risk assessment
Continuously verify and update your organization's security posture with automated, ongoing penetration testing and risk assessment.
Leverage advanced attack techniques at scale to rapidly test targets and uncover high-impact risks without manual intervention.
Expand security validation and enhance team efficiency in remote attack-and-defense operations with our collaborative platform.
Prioritize vulnerabilities by measuring actual risk and potential business impact using our advanced analytics and scoring system.
Discover and map your organization's attack surface, then identify the optimal remediation path based on actual risk exposure.
Our platform combines cutting-edge technology with comprehensive security testing capabilities
Access to an extensive and continuously updated database of known vulnerabilities, exploits, and security weaknesses across all platforms and systems.
Advanced verification components that eliminate false positives and confirm actual security vulnerabilities with precision and accuracy.
Comprehensive library of exploit modules for testing security vulnerabilities across diverse systems, applications, and network configurations.
AI-powered decision engine that analyzes security data, prioritizes risks, and recommends optimal remediation strategies.
Classification of Test Target - Comprehensive coverage across all major technology categories
| No. | Test Target | No. | Test Target |
|---|---|---|---|
| 1 | Office Systems | 11 | Intelligent Systems |
| 2 | Email Systems | 12 | Mobile Devices |
| 3 | Centralized Management Devices | 13 | Industrial Control Systems (ICS) |
| 4 | CMS | 14 | Forum Systems |
| 5 | Development Framework | 15 | Communication System |
| 6 | Network Devices | 16 | Big Data Platforms |
| 7 | Operating Systems (Windows, Linux) | 17 | Containers |
| 8 | Database | 18 | Virtualization Platforms |
| 9 | Application Servers | 19 | Cloud Computing |
| 10 | WEB Middleware | 20 | IOT System |
First Trial: $9.9 per Test
Ready to enhance your security posture with automated penetration testing? Contact our team to discuss how HackBox can protect your organization from evolving threats.