

HackBox (Virtual Attacker Bot) is an automated penetration testing platform that integrates AI with both offensive and defensive cybersecurity techniques.
By simulating real-world attacks, HackBox empowers organizations to proactively identify and address exploitable vulnerabilities within their digital assets — before malicious actors can exploit them. This offensive simulation approach enhances cyber resilience, provides a tactical edge in threat response, and significantly reduces network security risks for enterprise operations.
Comprehensive automated penetration testing capabilities
that simulate
real-world attack scenarios
Automatically identifies attack vectors such as open ports and services, web fingerprints, URLs, admin login portals, and file upload interfaces.
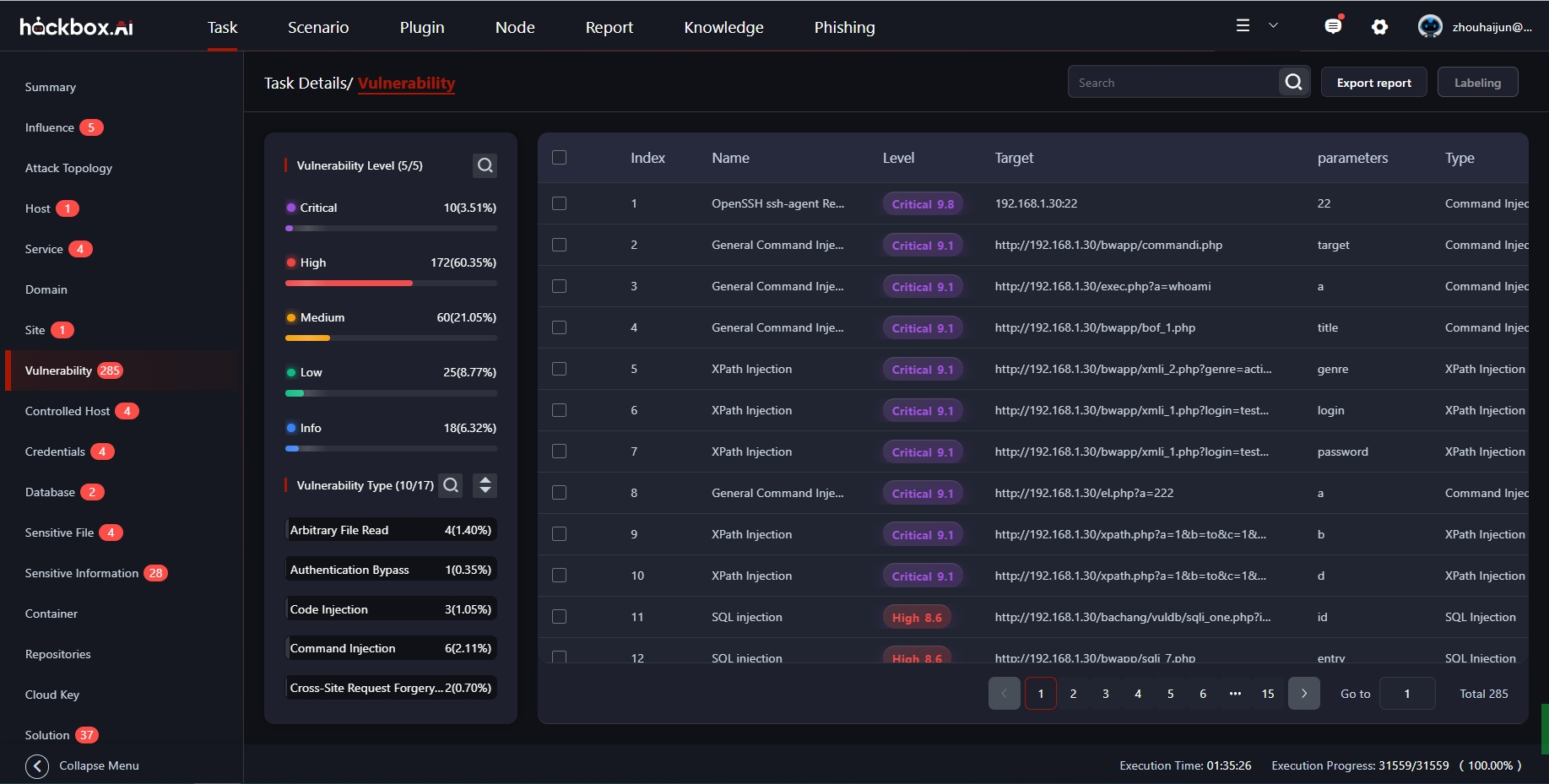
Automatically detects and verifies various vulnerabilities of the system and web application, eliminating false positives and confirming actual security weaknesses.
Automatically generate vulnerability exploit payloads to simulate real-world attacks, realizing simulated attacks on target systems and conducting risk forensics.
Employs autonomous decision-making to explore all possible attack paths, executing iterative exploits and lateral movement across the environment.
Visualizes the full attack chain, clearly illustrating the penetration process and pinpointing critical risk areas with actionable insights and remediation recommendations.
Based on vulnerability-driven principles, the system accurately detects and verifies a wide range of vulnerabilities, ensuring reliable results and generating high-quality penetration testing reports for users.
The automated penetration testing is powered by an AI engine that autonomously analyzes collected information and dynamically determines the next steps, including attack paths and actions, throughout the testing process.
Based on the data generated during the penetration testing process, the entire attack lifecycle is reconstructed and presented in a visualized manner, offering an intuitive depiction of both the overall attack landscape and detailed procedural steps.
Based on the data, privileges, and actual outcomes obtained through penetration testing, conduct a quantitative evaluation of risk and provide recommendations on the prioritization of vulnerability remediation.
Experience firsthand how our automated penetration testing platform can identify vulnerabilities and simulate real-world attacks to strengthen your security posture.